Seguridad Mania.com - España y América Latina
Portal sobre tecnologías para la seguridad física
- Destacamos »
- software Anti Blanqueo
LONDON -- (Marketwire) -- 01/29/13 -- Secure cloud hosting company, FireHost, has today announced its Q4 2012 Web application attack statistics, detailing the type and number of cyberattacks blocked by its servers in the U.S. and Europe between October and December 2012. Throughout 2012, FireHost has blocked over 64 million malicious cyberattacks of all types, with Cross-Site Scripting being the most prolific 'Superfecta' attack type overall.
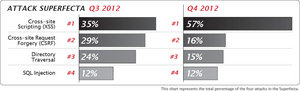
Each quarter, FireHost reports on the Superfecta -- a group of four cyberattacks that are the most dangerous -- and warns that both Cross-Site Scripting and SQL Injection attacks have become even more prevalent since the third quarter of 2012. The four attack types which make up the Superfecta, and which pose the most serious threat to the private information hosted in your database are Cross-site Scripting (XSS), Directory Traversal, SQL Injection, and Cross-site Request Forgery (CSRF).
Three out of the four Superfecta attack types rose in total count between Q3 and Q4 2012 -- only Cross-site Request Forgery attacks saw a drop in volume. However, the large increase in Cross-Site Scripting attacks, which rose from just over one million in Q3 2012 to 2.6 million in Q4, -- an increase of more than 160 percent -- seemingly dwarfs the other three attack types with 57 percent of the Superfecta. Cross-site scripting involves the insertion of malicious code into webpages in order to manipulate website visitors. It is used by attackers for a range of reasons, from simply interfering with websites to launching phishing attacks against web users.
"The change in frequency of the types of attack between quarters gives you an idea of how cybercriminals are constantly working to identify the path of least resistance," said Chris Hinkley, CISSP -- a senior security engineer at FireHost. "During Q4, ecommerce sites in particular would have been very busy with Christmas sales. Hackers will rapidly go after these high value targets with attacks that are highly automated and, if they are not yielding useful payloads, the attackers are equipped to quickly try a different type of attack. This is why it is important to have an understanding of the kind of traffic that is accessing your hosted infrastructure, so that you can make sure that malicious traffic is diverted and that there is less risk to sensitive data."
Throughout the whole year, FireHost blocked over 64 million malicious cyberattacks of all types, with Cross-Site Scripting being the most prolific Superfecta attack type overall, clocking in at 5.4 million blocked attacks.
As in Q3 2012, Europe is still the second most likely origin point for malicious traffic blocked by FireHost after North America, being the source of 13 percent of attacks. However, other regions have seen marked increases in the amount of attacks that are emanating from them, including Africa, Australia, and the Middle East. South and Central America were both the source of less malicious traffic between the most recent quarters.
Kevin Mitnick, a world renowned public speaker, author, and consultant on computer security issues has relied on FireHost to protect his own website since 2009. In the last year alone, FireHost has mitigated 108,000 malicious attempts against the hosting environment, a significant number of which fall into the Superfecta categories.
"It's good to know that FireHost is staying on top of these security threats and it's clear that their team is working very hard to protect customers against these attack vectors which are threatening them every minute," said Mitnick. "The escalating increase of XSS attacks in Q4 does not surprise me -- any teenager with a web application scanner can initiate these attacks in their free time. This increase does show, however, that when your servers are plugged in they are going to be probed -- likely within several minutes or so -- and that it's really important to work with a hosting provider like FireHost who can exercise due diligence on your behalf and keep you from being compromised."
The risks to businesses from the Superfecta varies and depends upon the kind of data that could be stolen in the event of a successful attack, according to Todd Gleason, director of technology at FireHost. "It's fairly obvious that, if you are a retailer or service provider dealing with private customer data or payment card details, your business will present an attractive target for hackers. That being said, we also see attacks that have the potential to simply deface or interfere with and disrupt websites and applications. Even though no data is lost, the reputation of a company can still be seriously damaged."
For more information about secure cloud hosting, please visit: http://www.firehost.com
About FireHost
FireHost is a secure cloud hosting company focused on protecting companies' sensitive data and brand reputations with an infrastructure built for security, scalability and performance. Customers with specific compliance or performance needs subscribe to FireHost's PCI, HIPAA or high traffic solutions, including some of the largest companies in the world as well as many fast growing eCommerce, SaaS and healthcare IT providers. FireHost provides services from Dallas, Phoenix, London and Amsterdam. http://www.firehost.com.
Follow FireHost on Twitter and the FireHost blog:
twitter.com/firehost
www.fireblog.com
Image Available: http://www2.marketwire.com/mw/frame_mw?attachid=2213414
Image Available: http://www2.marketwire.com/mw/frame_mw?attachid=2213412
Add to Digg Bookmark with del.icio.us Add to Newsvine
Media Contact:
FireHost
Sarah Hawley
Ubiquity Public Relations
Email Contact
480.292.4640
Publicamos interesante Informe de más de 48 págs y varios videos demostrativos sobre los posibles ataques a los robots de montaje de las fábricas. ... Leer más ►
Publicado el 22-Jun-2017 • 10.48hs
Publicado el 20-Jun-2017 • 20.22hs
Dirigido tanto a los principiantes, como a los expertos en seguridad informática y sistemas de control industrial (ICS), este libro ayudará a los lectores a comprender mejor la protección de normas de control interno de las amenazas electrónicas. ... Leer más ►
Publicado el 3-Ene-2012 • 20.16hs
Publicado el 25-Set-2009 • 01.26hs
Publicado el 17-Dic-2008 • 08.32hs
Publicado el 11-Oct-2016 • 12.48hs
Publicado el 15-Mar-2016 • 11.59hs
Publicado el 2-Feb-2017 • 11.38hs
Publicado el 20-Jun-2014 • 17.17hs
Publicado el 31-May-2011 • 05.13hs
Publicado el 25-Set-2008 • 17.54hs
Publicado el 1-Set-2016 • 16.11hs
Publicado el 31-Ago-2016 • 18.53hs
Publicado el 19-Ene-2017 • 15.47hs
Publicado el 4-Jul-2016 • 18.51hs